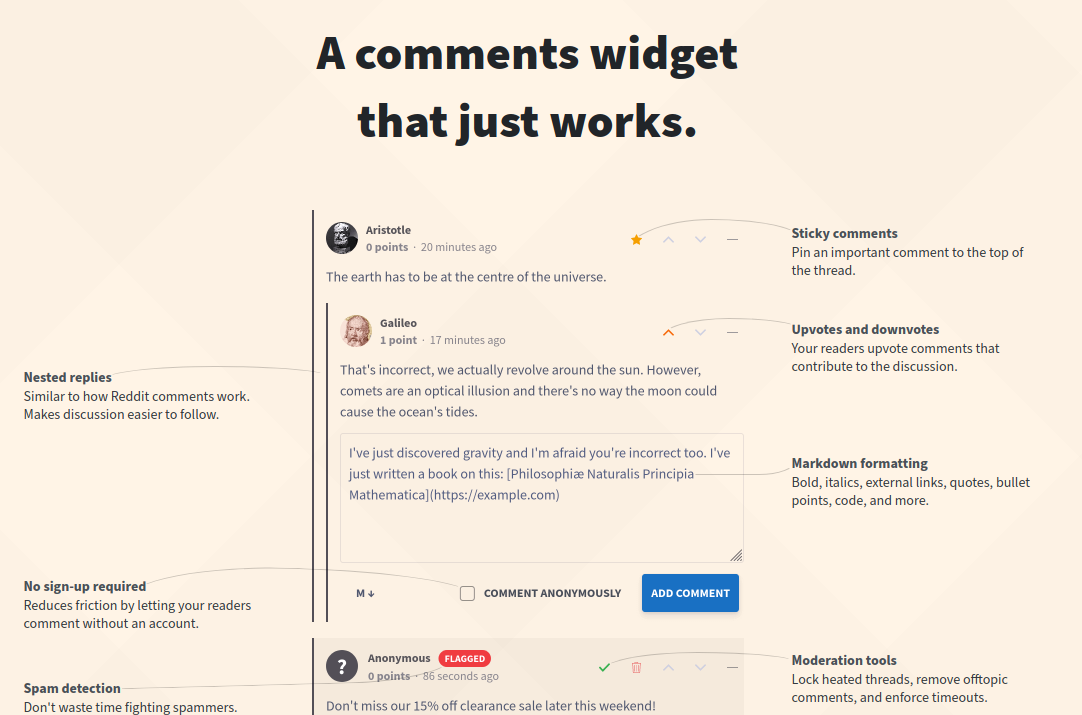
Commento is open-source privacy-focused commenting platform, It’s fast, bloat-free and can be self-hosted. This article guide you to install required dependencies like PostgreSQL (Ubuntu 20.04), setting up required Commento configuration and it’s SystemD to start the server automatically on when the system boot up. Additionally (but recommended), use Nginx as reverse proxy to serve Commento instance using HTTPS.
UPDATES:
WARNING: I’ve been using Commento for a long time, but since 1 year ago until this article was written, I didn’t find any updates or commits to their git master repository. You can try Commento++ as replacement.
Hardware requirements
Commento is pretty lightweight, but it’s recommend having at least 64MB of free RAM and at least 30MB of free disk space. This requirement does not include the requirements for running the PostgreSQL server. You may, of course, choose to use a separate server or a cloud PostgreSQL provider for the database.
Commento binary release has been verified to be working on the following hardware architectures: amd64, x86.
Software requirements
To run Commento, you need to have a PostgreSQL database version 9.6 or later. There aren’t any other software requirements, unless you’re compiling from source.
Install PostgreSQL
Let’s assume you use Ubuntu 20.04 which provide PostgreSQL >= 9.6 from their official repository package.
To install PostgreSQL, first refresh your server’s local package index:
1sudo apt update
Then, install the Postgres package along with a -contrib package that adds some additional utilities and functionality:
1sudo apt install postgresql postgresql-contrib
By default, Postgres uses a concept called roles to handle authentication and authorization. These are, in some ways, similar to regular Unix-style users and groups.
Upon installation, Postgres is set up to use ident authentication, meaning that it associates Postgres roles with a matching Unix/Linux system account. If a role exists within Postgres, a Unix/Linux username with the same name is able to sign in as that role.
The installation procedure created a user account called postgres that is associated with the default Postgres role. There are a few ways to utilize this account to access Postgres. One way is to switch over to the postgres account on your server by running the following command:
1sudo -i -u postgres
Creating a New Role
If you are logged in as the postgres account, you can create a new role by running the following command:
1createuser --interactive
If you prefer to use sudo for each command without switching from your normal account, run:
1sudo -u postgres createuser --interactive
1Enter name of role to add: commento
2Shall the new role be a superuser? (y/n) n
3Shall the new role be allowed to create databases? (y/n) n
4Shall the new role be allowed to create more new roles? (y/n) n
Creating a New Database
Another assumption that the Postgres authentication system makes by default is that for any role used to log in, that role will have a database with the same name which it can accessed.
This means that if the user you created in the last section is called ditatompel, that role will attempt to connect to a database which is also called ditatompel by default. You can create the appropriate database with the createdb command.
If you are logged in as the postgres account, you would type something like the following:
1createdb commento
If, instead, you prefer to use sudo for each command without switching from your normal account, you would run:
1sudo -u postgres createdb commento
Create User Password
1sudo -u postgres psql
1ALTER USER postgres PASSWORD '[ChangeThisWithYourSecretPassword]';
If successful, Postgres will output a confirmation of ALTER ROLE as seen above.
Download Commento Binary
Find the latest Commento release binary archive from the releases page and download it to your server.
1wget https://dl.commento.io/release/commento-v1.8.0-linux-glibc-amd64.tar.gz
Extract to desired Commento installation, in this example /opt/commento.
1mkdir /opt/commento
2tar -xvzf commento-v1.8.0-linux-glibc-amd64.tar.gz -C /opt/commento/
Launching Commento
You need to set up some required configuration before starting Commento and optionally additional configuration like SMTP and OAuth. In this example, let’s assume our Commento instance will be running on server localhost port 8088 and will be available at https://commento.ditatompel.com via Nginx reverse proxy.
Before you launch Commento, you will also need a usable PostgreSQL server. Let’s say the server is available at localhost on port 5432 using database named commento with the user credentials commento and password commentoPassword.
Set up the environment variables to start the Commento server on 127.0.0.1 on port 8088. You can create .env file under /etc/commento/commento.env for easier management.
1COMMENTO_ORIGIN=https://commento.ditatompel.com
2#COMMENTO_CDN_PREFIX=https://commento.ditatompel.com
3# Set binding values
4COMMENTO_BIND_ADDRESS=127.0.0.1
5COMMENTO_PORT=8088
6
7# Set PostgreSQL settings
8COMMENTO_POSTGRES=postgres://commento:[email protected]:5432/commento?sslmode=disable
9
10#
11# Below configuration is optional
12# Uncomment and edit to fit your needs
13#
14
15# Prevent registration
16#COMMENTO_FORBID_NEW_OWNERS=false # default true
17
18# If set to true, all static content will be served GZipped if the client's browser supports compression. Defaults to false.
19#COMMENTO_GZIP_STATIC=true
20
21
22# Set the SMTP credentials
23#COMMENTO_SMTP_HOST=mail.example.com
24#COMMENTO_SMTP_PORT=587
25#[email protected]
26#COMMENTO_SMTP_PASSWORD=examplePassword
27#[email protected]
28
29# Set Google OAuth credentials
30#COMMENTO_GOOGLE_KEY=some-random-string-key.apps.googleusercontent.com
31#COMMENTO_GOOGLE_SECRET=somerandomsecret
Set COMMENTO_CDN_PREFIX to the appropriate URL if you are serving static content from a CDN. Otherwise, set it to the same value as COMMENTO_ORIGIN.
Then, create systemd service file located on /etc/systemd/system/commento.service:
1[Unit]
2Description=Commento daemon service
3After=network.target postgresql.service
4
5[Service]
6Type=simple
7ExecStart=/opt/commento/commento
8Environment=COMMENTO_CONFIG_FILE=/etc/commento/commento.env
9
10[Install]
11WantedBy=multi-user.target
Reload systemd unit files configuration and start Commento service.
1sudo systemctl daemon-reload
2sudo systemctl start commento
3sudo systemctl enable commento
Setting up Nginx reverse proxy for Commento (sub)domain
Now, time to configure Nginx in front of Commento. Nginx server block configuration below is basic example to use Nginx as reverse proxy to serve Commento using SSL (HTTPS).
1server {
2 listen 80;
3 server_name commento.ditatompel.com;
4 root /var/www/default;
5 # in case you use certbot...
6 location /.well-known/acme-challenge/ { allow all; }
7 location / { return 301 https://$host$request_uri; }
8}
9
10server {
11 listen 443 ssl http2;
12 server_name commento.ditatompel.com;
13
14 # Edit to fit with your server environment and path
15 ssl_certificate /path/to/your/cert/fullchain.pem;
16 ssl_certificate_key /path/to/your/cert/privkey.pem;
17 ssl_dhparam /path/to/your/cert/dhparam.pem;
18 ssl_session_timeout 1d;
19 ssl_session_cache shared:SSL:10m;
20 ssl_session_tickets off;
21 ssl_protocols TLSv1.2 TLSv1.3;
22 ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384;
23 ssl_prefer_server_ciphers off;
24
25 root /var/www/default;
26
27 location / {
28 proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
29 proxy_set_header X-Forwarded-Proto $scheme;
30 proxy_set_header X-Real-IP $remote_addr;
31 proxy_set_header Host $http_host;
32 proxy_pass http://127.0.0.1:8088/;
33 }
34}
Restart Nginx service and try to access your Commento instance.